Cloudflare Help Center
Articles in this section
Connect with the Cloudflare Community
More on this topic: Discussions and Tips
Connect with the Cloudflare Community
Configuring URL forwarding or redirects with Cloudflare Page Rules
Learn how to set up URL forwarding or redirects with Cloudflare.
Overview
You can define a page rule to forward or redirect traffic to a different URL using the Rules app in the Cloudflare dashboard.
Forwarding examples
Imagine you want site visitors to easily reach your website for a variety of URL patterns. For instance, the Page Rule URL patterns *www.example.com/products and *example.com/products match:
but do not match: Once you have created the pattern that matches what you want, click the Forwarding toggle. That exposes a field where you can enter the address I want requests forwarded to. If I enter the address above in the forwarding box and click Add Rule, within a few seconds any requests that match the pattern I entered will automatically be forwarded with a 302 Redirect to the new URL.
Advanced forwarding options
If you use a basic redirect, such as forwarding the root domain to www.example.com, then you lose anything else in the URL.
To fix the forwarding from the root to www in the above example, you could use the same pattern: You’d then set up the following URL for traffic to forward to: In this case, if someone went to: They’d be redirected to:
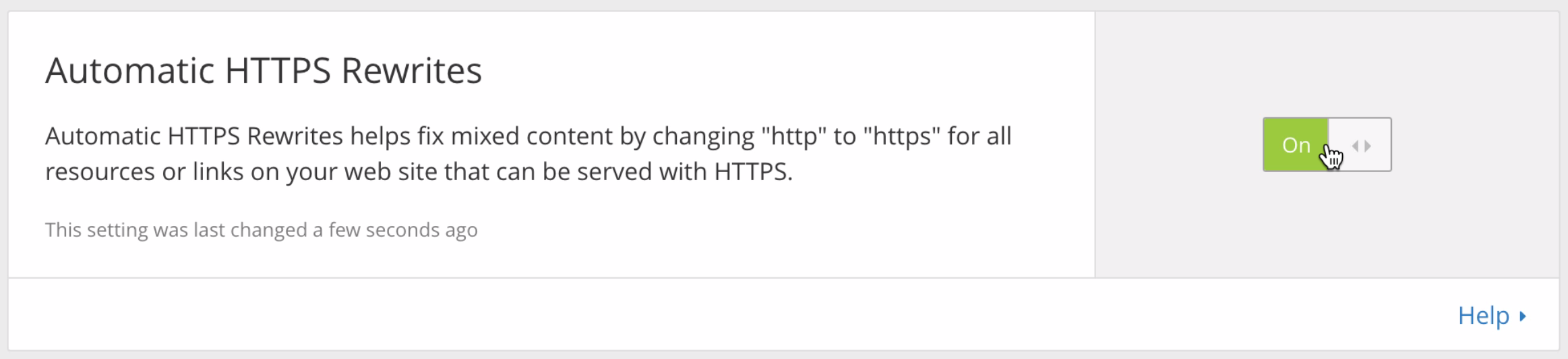
Automatic HTTPS Rewrites
Solving the mixed content problem
Is your website having issues with mixed content? Automatic HTTPS Rewrites offers a one-click solution that can safely eliminate mixed content by rewriting insecure URLs dynamically from known (secure) hosts. Automatic HTTPS Rewrites is available on all Cloudflare plans. Sign up for a Cloudflare plan today and eliminate mixed content today.
Transitioning to fully secure content
For most visitors the green padlock next to your URL makes them feel safe when entering a password or credit card number on your website. The green padlock has become the symbol for a secure website where all traffic to and from the domain is encrypted and protected from prying eyes.
Cloudflare has aimed at putting an end to insecure, unencrypted Internet traffic. Universal SSL has made switching from http:// to https:// as easy as clicking a button, Origin CA has driven the price of a SSL certificate for your server down to zero, and Dedicated Certificates offers turnkey SSL certificate management eliminating most of the maintenance tasks associated with traditional SSL certificates.
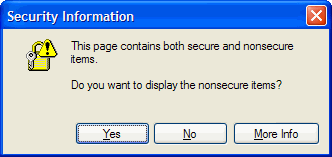
In 1997, Internet Explorer 3.0.2 warned users of sites with mixed content with this dialog box.
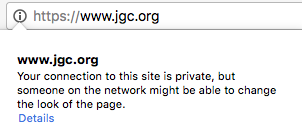
Today, Google Chrome shows a circled i on any https:// that has insecure content.
Despite these various options, there are still a number of websites that have found enabling SSL difficult and error prone. Identifying and correcting resources that are hard-coded to be loaded over HTTP can be challenging in legacy applications and online publishing platforms. Reliance on 3rd party content and functionality outside domain control can make corrective actions almost impossible.
When websites send both secure (https://) and nonsecure (http://) content from the same page they end up with a problem known as mixed content. When you serve mixed content, the unencrypted resources eliminate the green padlock next to your URL while exposing that data to eavesdropping and tampering vulnerabilities.
Finding and fixing mixed content can be a very challenging and time consuming task. Cloudflare eliminates the manual process of updating resource paths by offering a one click solution; Automatic HTTPS Rewrites.
Automatic HTTPS Rewrites safely eliminates mixed content issues by rewriting insecure URLs dynamically from known secure hosts to their secure counterpart. Cloudflare maintains a list of known secure hosts that includes the Electronic Frontier Foundation excellent HTTPS Everywhere extension and Google Chrome HSTS preload list.
By enforcing a secure connection, Automatic HTTPS Rewrites enables you to take advantage of the latest security standards and web optimization features like HTTP/2 and Server Push which is only available over HTTPS. Automatic HTTPS Rewrites eliminates errors in your visitor’s browser when loading content by loading secured content over unsecured, allowing them to see a green padlock next to your URL on their browser.
Is your website having issues with mixed content? Automatic HTTPS Rewrites is available on all Cloudflare plans, including Free. Sign up for a Cloudflare plan today and eliminate mixed content today.
Passive v. Active Mixed Content
Mixed content comes in two different categories: passive content and active content. The two different categories define the threat level each type of mixed content can pose if content is rewritten as part of a man-in-the-middle attack.
Passive mixed content refers to unencrypted content that cannot interact with other elements on the page (parts of the Document Object Model) thus posing a lower security threat compared to active content in a man-in-the-middle attack scenario. Tampering with passive content such as text, image, video and audio is limited to the content itself while the rest of the encrypted content on the page remains protected.
Active mixed content refers to unencrypted content that can has the ability to interact with other elements on the page compromising the security of the entire page. Active content includes elements such as iframes, scripts, stylesheets, Flash resources, and other elements that have attributes (e.g. src, href, url, and data) that can make HTTP requests to remote domains.
The risks associated with mixed content vary based on the type of mixed content you have and the data your web page may expose. While passive mixed content poses a lower threat than active mixed content, attackers are constantly finding new and creative ways to exploit vulnerable pages. Whether your mixed content is passive or active, Automatic HTTPS Rewrites offers a one click solution that safely eliminates mixed content issues by rewriting insecure URLs dynamically from known (secure) hosts.
Learn more about Automatic HTTPS Rewrites on our blog.
Setting Up Cloudflare Is Easy
Set up a domain in less than 5 minutes. Keep your hosting provider. No code changes required.
Cloudflare Pricing
Everyone’s Internet application can benefit from using Cloudflare.
Pick a plan that fits your needs.
Free Plan
for personal websites and blogs
We offer a Free plan for small personal websites, blogs, and anyone who wants to evaluate Cloudflare.
Our mission is to build a better Internet. We believe every website should have free access to foundational security and performance. Cloudflare’s Free plan has no limit on the amount of bandwidth your visitors use or websites you add.
If you want to make your site even faster and more resilient, you can easily upgrade to one of our higher tier plans.
Cloudflare Help Center
Articles in this section
Connect with the Cloudflare Community
More on this topic: Discussions and Tips
Connect with the Cloudflare Community
Troubleshooting redirect loop errors
Resolve redirect loop (too many redirects) errors that prevent visitors from viewing your website.
Overview
The two typical causes of redirect loop errors are:
Browsers typically display error messages when redirect loop errors occur, such as:
Cloudflare SSL options incompatible with your origin web server
The most common cause of redirect loops is due to a combination of
Cause
The Flexible SSL encryption mode in the Cloudflare SSL/TLS app Overview tab encrypts traffic between the browser and the Cloudflare network over HTTPS. However, when the Flexible SSL option is enabled, Cloudflare sends requests to your origin web server unencrypted over HTTP. Redirect loops occur if your origin web server is configured to redirect all HTTP requests to HTTPS when using the Flexible SSL option.
Redirect loops may also occur when using the Full or Full(strict) SSL option. The only difference is that Cloudflare contacts your origin web server over HTTPS and the redirect loop occurs if your origin web server redirects HTTPS requests to HTTP.
Resolution
Resolve redirect loops via one of the following methods:
Page Rule misconfiguration
Cause
Redirect loops also occur if two conflicting Page Rules are configured with Forwarding URL settings. For example, one Page Rule redirects traffic for a.example.com to b.example.com and another page rule redirects traffic for b.example.com to a.example.com.
Resolution
Check the rules in Rules > Page Rules to confirm if you have two rules configured to forward traffic to each other.
Как перенаправить сайт с HTTP на HTTPS?
HTTPS должен быть везде, и в последнее время Google рассматривает это как сигнал ранжирования для результатов своей поисковой системы.
Есть две основные причины, по которым вам следует подумать о защите своего сайта с помощью SSL-сертификата.
Если вас беспокоит стоимость, то позвольте напомнить вам, что вы можете получить SSL-сертификат БЕСПЛАТНО от многих эмитентов. И большая часть общего хостинга предлагает бесплатный SSL.
1. Перенаправление на HTTPS в Apache
Сконфигурированный веб-сайт должен иметь возможность перенаправления и доступа по https.
2. Перенаправление на HTTPS в Nginx
Войдите на веб-сервер Nginx и создайте резервную копию файла nginx.conf или default.conf файла (независимо от того, какой файл вы используете для директивы сервера)
Перезапустите Nginx, чтобы протестировать сайт.
3. Перенаправление на HTTP в Cloudflare
Если вы используете Cloudflare для повышения производительности и безопасности, то перенаправить веб-сайт через HTTPS очень просто.
Есть еще один способ, с помощью правила страницы.
Это займет несколько секунд, и у вас все настроено, чтобы ваш сайт был доступен через https.
4. Перенаправление на HTTPS в cPanel
Я предполагаю, что вы используете это на платформе общего хостинга. Во-первых, вы должны убедиться, что хостинг-провайдер предлагает SSL и включен для вашего сайта.
Примечание: если вы уже видите «RewriteEngine On» в существующем файле, вам не нужно дублировать его
5. Перенаправление на HTTPS в SUCURI
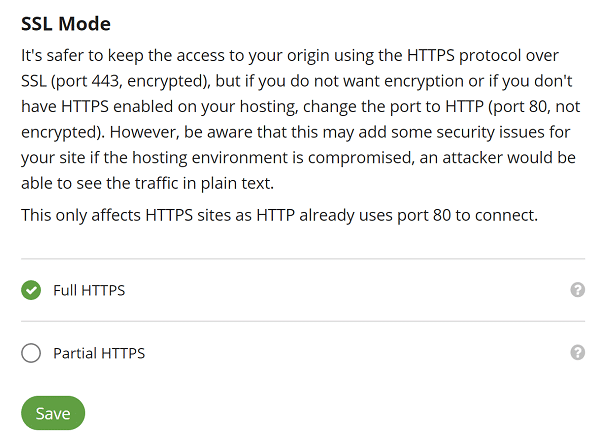
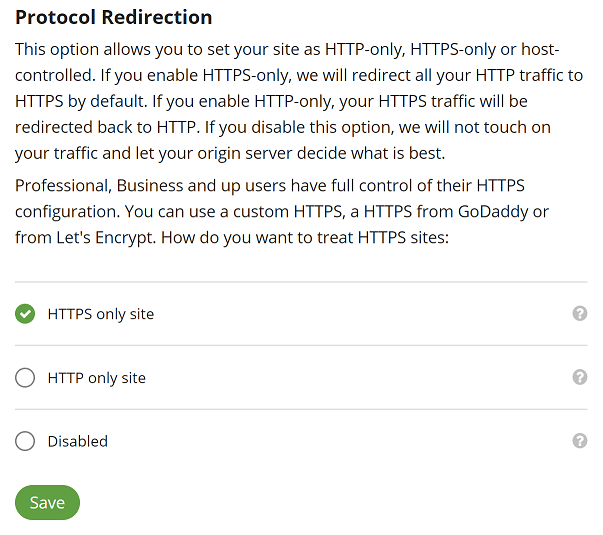
SUCURI предлагает БЕСПЛАТНЫЙ сертификат по плану WAF, и вы можете включить его, перейдя на вкладку HTTPS / SSL.
Сначала выберите Полный HTTPS (Full HTTPS) в режиме SSL.
Во-вторых, выберите HTTPS only site в перенаправлении протокола.
Сохраните конфигурацию, и через несколько секунд ваш сайт будет доступен через https.
Заключение
После настройки перенаправления убедитесь, что все ресурсы загружаются через HTTPS.
Cloudflare Help Center
Articles in this section
Connect with the Cloudflare Community
More on this topic: Discussions and Tips
Connect with the Cloudflare Community
More on this topic: Discussions and Tips
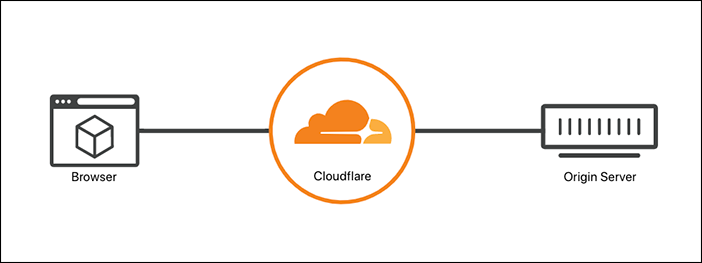
Understand which Cloudflare SSL options encrypt HTTPS traffic between Cloudflare and the origin web server.
Overview
The SSL section of the Cloudflare SSL/TLS app contains several options that determine whether Cloudflare securely connects to your origin web server.
After reviewing the description of each SSL option, refer to our list of recommended SSL options depending on your origin web server SSL configuration:
Off disables HTTPS for your site visitors whereas Full(Strict) provides the most traffic security end-to-end.
Off disables secure HTTPS connections between both visitors and Cloudflare and between Cloudflare and your origin web server. Visitors can only view your website over HTTP. Any connections attempted via HTTPS result in a HTTP 301 redirect to unencrypted HTTP.
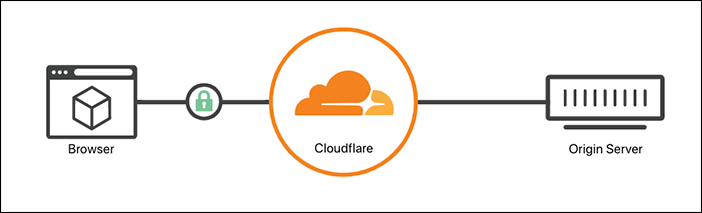
Flexible
The Flexible SSL option allows a secure HTTPS connection between your visitor and Cloudflare, but forces Cloudflare to connect to your origin web server over unencrypted HTTP. An SSL certificate is not required on your origin web server and your visitors will still see the site as being HTTPS enabled.
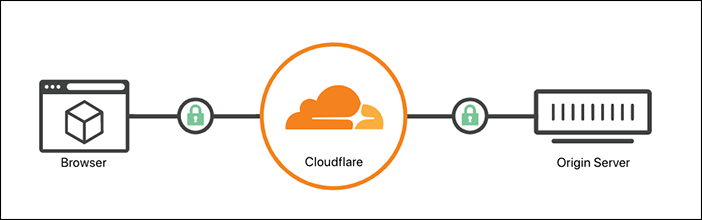
Full ensures a secure connection between both the visitor and your Cloudflare domain and between Cloudflare and your web server.
To avoid 525 errors, before enabling Full SSL option, configure your origin web server to allow HTTPS connections on port 443 and present either a self-signed SSL certificate, a Cloudflare Origin CA certificate, or a valid certificate purchased from a Certificate Authority.
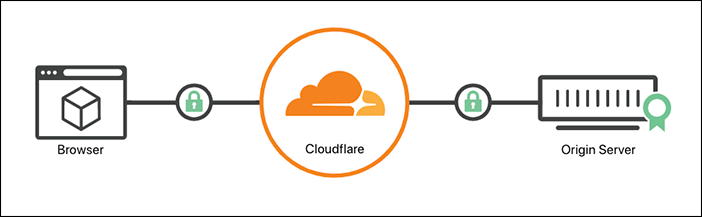
Full (strict)
Full (strict) ensures a secure connection between both the visitor and your Cloudflare domain and between Cloudflare and your origin web server. Full (strict) support SSL hostname validation against CNAME targets.
Configure your origin web server to allow HTTPS connections on port 443 and present either a Cloudflare Origin CA certificate or a valid certificate purchased from a Certificate Authority. This certificate must be signed by a Certificate Authority that is trusted by Cloudflare, have a future expiration date, and cover the requested domain name (hostname).
Strict (SSL-Only Origin Pull)
Strict (SSL-Only Origin Pull) instructs Cloudflare’s network to always connect to your origin web server using SSL/TLS encryption (HTTPS). The SSL certificate presented by the origin web server must be signed by a Certificate Authority that is trusted by Cloudflare, have a future expiration date, and cover the requested domain name (hostname).
SSL/TLS Recommender
Check if your domain could upgrade to a more secure SSL option by enabling SSL/TLS Recommender.
Recommender does the following to maximize security while preserving content:
When enabled, SSL/TLS Recommender sends the zone owner an email with an SSL option recommendation (if one is available). A Recommended by Cloudflare tag displays next to the recommended option on the SSL/TLS page. If you do not receive an email, keep your current option. You are not required to use the recommendation. Recommender runs periodically and sends notifications if new recommendations become available. Recommender will never recommend a weaker SSL option than what is currently configured.
SSL/TLS Recommender is not intended to resolve issues with website or domain functionality. Recommender is not compatible with all other Cloudflare features and will not be able to complete its scan and show the Recommended by Cloudflare tag if: